JSQL is a lightweight application that is inbuilt in Kali Linux but it is open source and platform.
independent (Windows, Linux, Mac OS X, Solaris). used to find database information from a distant server. This is another injection tool just like SQLMAP but is a lot more user friendly cause SQLMAP is command line based whereas JSQL is Graphical User Interface(GUI) Based. JSQL is more convenient and more easier to use as no commands will be used to perform injection. As JSQL is platform independent interested people can download it in their respective platform or can use it easily if they are using Kali Linux. In this tutorial i am going to use Kali Linux and JSQL is already installed in Kali Linux. JSQL is under Application-> Database Assessment-> JSQL Injection.

First thing that we will require is the URL of the website that we want to hack the database or perform SQL injection attack. We are going to use the same website that we used in SQLMAP tutorial that is http://testphp.vulnweb.com for demonstration purpose.
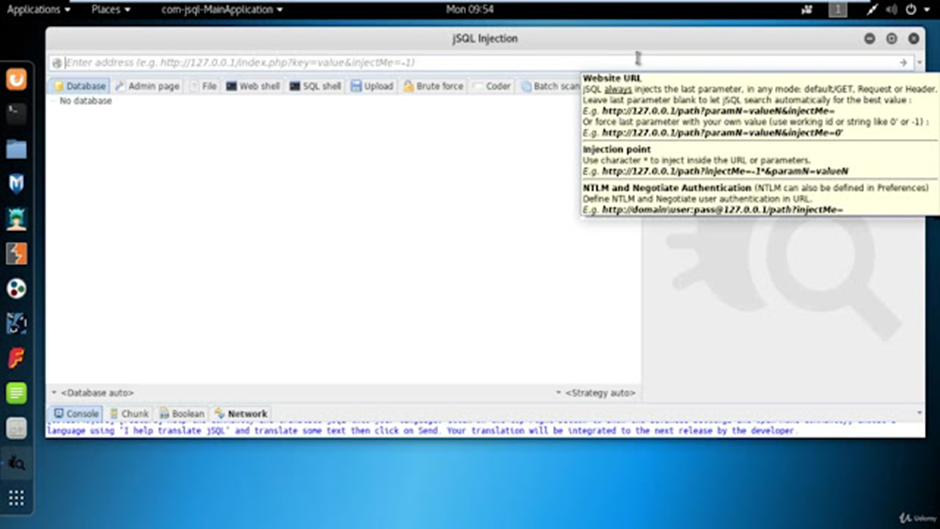
Put the URL of the website in the URL tab of the tool as per displayed in the picture. Once the URL is inserted we just have to click on the arrow to start the injection process. The actual procedure will happen in the background of the tool hence even non technical person can perform injection using this method. In case there is no result we have to do slight modification in the URL to obtain result.
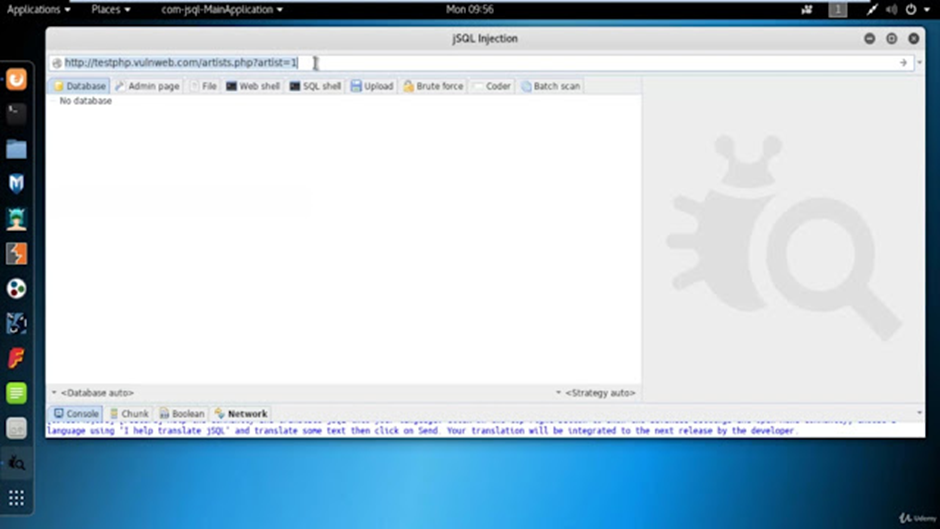
Normal Url:- http://testphp.vulnweb.com/artists.php?artist=1
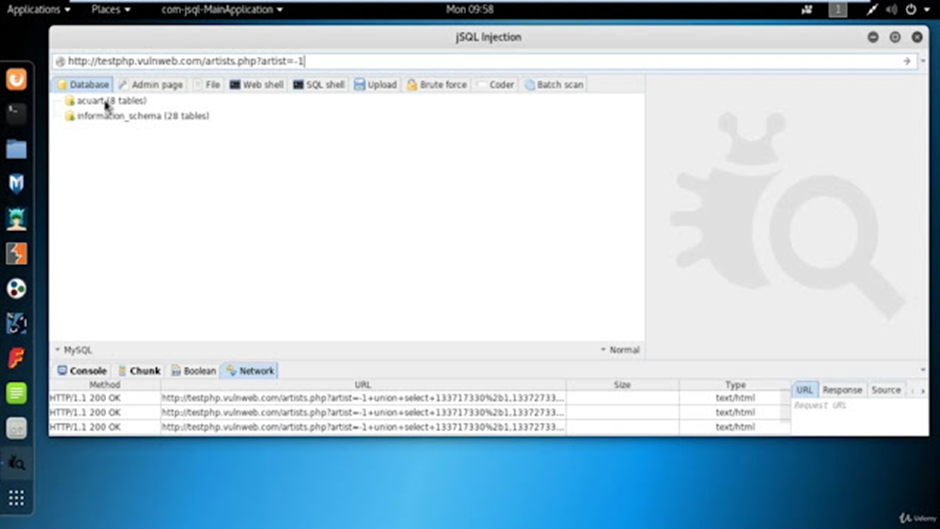
1st URL change Try:- http://testphp.vulnweb.com/artists.php?artist=-1
2nd URL change Try:- http://testphp.vulnweb.com/artists.php?artist=-1‘
3rd URL Change Try:- http://testphp.vulnweb.com/artists.php?artist=1‘ \
The changes in the URL can be done to get an output or get information about the website. I have already discussed this in detail in another SQL Injection tutorial. To get detail info about the URL change click here. Since everything is JSQL once the injection process gets completed we will get a result in the form of databases. We can then click on the respective database and access tables and respective columns as well with the help of mouse.
If we want to view the particular column then we can do it by marking the particular column with a check mark and then right click on the table and then load. It will show the data inside that particular column.

Similarly we can do it with any column of our choice. It is a very simple task that can be done by anyone. As i have already told in my previous SQL injection articles different people use SQL injection for different purposes, so it literally depends upon the attackers perspective. If SQL injection attack is done by a hacker then it can be for a harmful purpose of either stealing or damaging the data, if performed by an ethical hacker or penetration testers can be used for vulnerability assessment , penetration testing or even finding loopholes in the website.
